In today’s internet world, security is not optional—it’s a necessity. Every time you log in to a website, make a payment, or even submit a simple contact form, you’re sending data across the internet. Without protection, that data can be intercepted, stolen, or altered.
That’s where SSL/TLS comes in—two security protocols that encrypt communication between your browser and a website’s server. In this guide, we’ll dive deep into what SSL/TLS is, its history, how it works, the handshake process, types of encryption, certificates, and why every website needs it.

1. Introduction to SSL/TLS
SSL (Secure Sockets Layer) and TLS (Transport Layer Security) are protocols used to secure communication over the internet. They make sure that:
- The data you send is encrypted (so no one else can read it).
- The website you’re visiting is authentic (not a fake).
- The data remains unchanged during transfer.
When you see a padlock icon in your browser’s address bar and the website starts with HTTPS, it means SSL/TLS is in action.
2. History of SSL/TLS
The journey of SSL/TLS started in the mid-1990s:
- SSL 1.0 – Developed by Netscape but never released publicly due to security flaws.
- SSL 2.0 – Released in 1995 but had serious vulnerabilities.
- SSL 3.0 – Released in 1996, a big improvement, but later found vulnerable (POODLE attack).
- TLS 1.0 – Introduced in 1999 as an upgrade to SSL.
- TLS 1.1 & 1.2 – Added stronger encryption and better performance.
- TLS 1.3 – Latest version (2018) with faster and more secure connections.
Today, SSL is mostly outdated, and TLS is the modern standard.
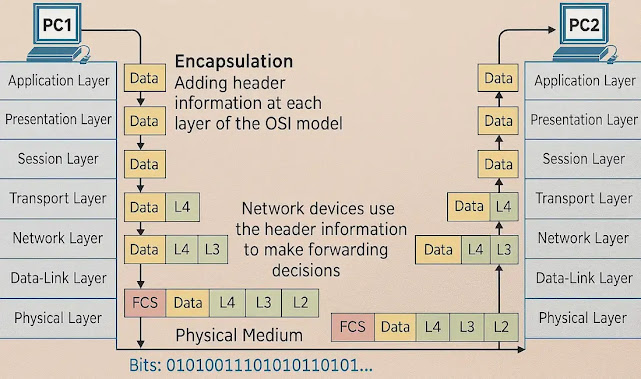
3. How SSL/TLS Works
At its core, SSL/TLS uses encryption to protect data. Here’s the basic idea:
- You connect to a secure website.
- The website shows proof of its identity using an SSL/TLS certificate.
- Your browser and the website agree on a secure encryption method.
- All data is scrambled before sending and unscrambled upon receiving.
This ensures that even if someone intercepts the data, they can’t understand it.
4. Step-by-Step: SSL/TLS Handshake Process

The SSL/TLS handshake is how your browser and the website’s server agree on encryption before sending data.
Step 1: Client Hello – Your browser sends a message to the server with supported encryption methods.
Step 2: Server Hello – The server responds with its chosen encryption method and sends its SSL/TLS certificate.
Step 3: Certificate Validation – Your browser checks the certificate against trusted Certificate Authorities (CAs).
Step 4: Key Exchange – Using asymmetric encryption, a shared session key is generated.
Step 5: Secure Communication – All data is now encrypted using symmetric encryption for speed.
Want a deeper, step-by-step walkthrough of the SSL/TLS handshake process? Read our full guide here .
5. Types of Encryption in SSL/TLS
- Symmetric Encryption – Same key is used to encrypt and decrypt data (fast, used after handshake).
- Asymmetric Encryption – Uses a public key (shared) and a private key (kept secret) to exchange session keys securely.
- Hashing – Creates a digital fingerprint of data to ensure integrity (e.g., SHA-256).
6. Components of an SSL/TLS Certificate
An SSL/TLS certificate contains:
- Domain name (e.g., firewallflow.com)
- Issuer (Certificate Authority)
- Validity period (start and expiry date)
- Public key
- Signature algorithm
- Certificate fingerprint
7. What Are Public and Private Keys?
Public Key – Shared openly and used to encrypt data.
Private Key – Kept secret on the server and used to decrypt data.
Without the private key, encrypted data can’t be read.
8. Why Websites Need SSL/TLS Certificates
- Data Protection – Prevents hackers from intercepting sensitive information.
- Trust & Credibility – Visitors see the padlock and feel safe.
- SEO Boost – Google gives ranking preference to HTTPS sites.
- Required for Payments – PCI DSS compliance for e-commerce.
- Avoid Browser Warnings – Chrome, Firefox, and Edge block HTTP sites.
9. Types of SSL/TLS Certificates
By Validation Level:
- DV (Domain Validation) – Verifies domain ownership (fast, basic).
- OV (Organization Validation) – Verifies business identity.
- EV (Extended Validation) – Shows company name in browser bar (highest trust).
By Domain Coverage:
- Single Domain – Protects one domain.
- Wildcard – Protects a domain and all subdomains.
- Multi-Domain (SAN) – Protects multiple domains.
10. Certificate Authority (CA)
A Certificate Authority issues SSL/TLS certificates after verifying the domain or organization. Examples:
- DigiCert
- Sectigo
- Let’s Encrypt (Free)
- GlobalSign
They maintain trust by being included in browser root certificate stores.
11. Self-Signed Certificates
A self-signed certificate is created and signed by the website owner instead of a trusted CA.
- Pros: Free, quick for testing.
- Cons: Not trusted by browsers, causes warnings.
- Use Case: Internal servers, development environments.
12. How to Get an SSL/TLS Certificate for Your Website
- Choose a CA (e.g., Let’s Encrypt, DigiCert).
- Generate a CSR (Certificate Signing Request) on your server.
- Submit CSR to CA for verification.
- Download and Install the certificate.
- Test your SSL setup using tools like [SSL Labs Test](https://www.ssllabs.com/ssltest/).
13. Advantages of Using SSL/TLS
- Strong encryption for data.
- Increased trust from visitors.
- SEO ranking benefits.
- Compliance with data protection laws.
14. Common Myths About SSL/TLS
Myth: SSL makes my site 100% secure.
Fact: It only secures data in transit, not your site from hacking.
Myth: Free SSL is unsafe.
Fact: Free SSL from trusted CAs is as secure as paid ones.
Myth: SSL slows down websites.
Fact: TLS 1.3 is extremely fast.
15. Future of SSL/TLS
TLS 1.3 offers faster handshakes and better security.
Work is ongoing on post-quantum encryption to prepare for future threats.
16. Conclusion
SSL/TLS is the foundation of secure communication on the internet. From encrypting sensitive data to building trust with visitors, it’s a must-have for every website owner. If your site isn’t using HTTPS yet, it’s time to make the switch—your visitors (and Google) will thank you.
17. FAQs
Q1: Is SSL the same as TLS?
No, TLS is the newer, more secure version of SSL.
Q2: How do I check if a website has SSL/TLS?
Look for the padlock icon and “https://” in the browser.
Q3: Can I get SSL for free?
Yes, from providers like Let’s Encrypt.
Q4: What happens if my SSL certificate expires?
Visitors will see a security warning, and some may be blocked from your site.
Q5: Is HTTPS enough to secure my website?
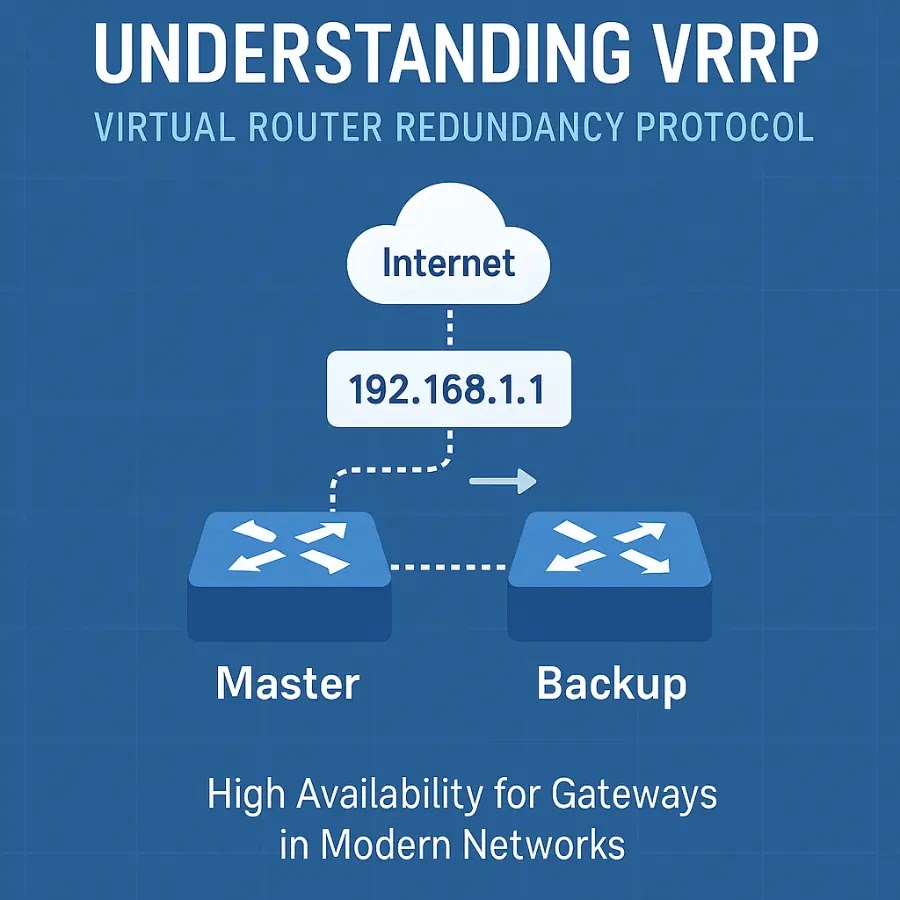
No, you still need other security measures like firewalls, WAFs, and malware protection.
📚 Read More from FirewallFlow
🔗 Outside Source: To explore SSL/TLS in greater detail, check out the official Cloudflare Learning Center – What is SSL?.
Cybersecurity blogger with a focus on firewalls, network security, and tech trends making security simple for everyone, from IT pros to curious minds.